PuTTY’s copy and paste works entirely with the mouse. In order to copy text to the clipboard, you just click the left mouse button in the terminal window, and drag to select text. When you let go of the button, the text is automatically copied to the clipboard. You do not need to press Ctrl-C or Ctrl-Ins; in …
Category : FACT
30 posts
What is Proxy Server? In computer networks, a proxy server is a server (a computer system or an application) that acts as an intermediary for requests from clients seeking resources from other servers.[1] A client connects to the proxy server, requesting some service, such as a file, connection, web page, or other resource available from …
How to Prevent Cross-site Scripting (XSS) – Generic Tips Preventing Cross-site Scripting (XSS) is not easy. Specific prevention techniques depend on the subtype of XSS vulnerability, on user input usage context, and on the programming framework. However, there are certain general strategic principles that you should follow to keep your web application safe. 1 Step …
You’ve launched your website and done all you can to ensure its success, but you may have overlooked a critical component: website security. Cyberattacks cause costly clean-up, damage your reputation, and discourage visitors from coming back. Fortunately, you can prevent it all with effective website security. We’ll discuss the basics of website security and what solutions will help ensure your …
Cross-site Scripting (XSS) Cross-site Scripting (XSS) is a client-side code injection attack. The attacker aims to execute malicious scripts in a web browser of the victim by including malicious code in a legitimate web page or web application. The actual attack occurs when the victim visits the web page or web application that executes the malicious …
What is a payment gateway and how does it work? A payment gateway is an application that makes the entire process of online payment more streamlined and secure. It acts as a secure link between your website or application and the bank. The role of payment gateway begins when a customer wishes to purchase on …
APIs have become omnipresent in the world of software and mobile app development. Right from private solutions to public-facing services apps and partner integrations, it is present everywhere. They are helping developers in creating apps that caters to diverse set of customer needs. They are transforming the architectural patterns with much sophisticated approach of mobile …
What are Barcodes? A barcode is a method of representing data in a visual format of machine-readable information about the item to which it is attached. A barcode represent data by varying in widths and spacing of parallel lines. Nowadays, the barcode is referred to as a linear or 1-dimensional code, that can be scanned …
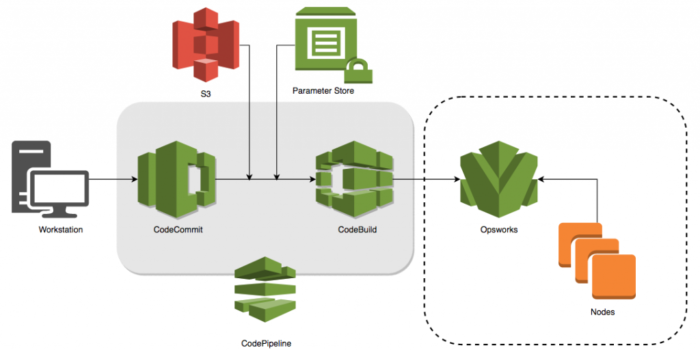
Introduction Amazon Web Services (AWS) has an extremely wide variety of services which cover almost all our infrastructure requirements. Among the given services, there is AWS Systems Manager which is a collection of services to manage AWS instances, hybrid environment, resources, and virtual machines by providing a common UI interface for all of them. Services …
The OpenVPN protocol is responsible for handling client-server communications. Basically, it helps establish a secure “tunnel” between the VPN client and the VPN server. When OpenVPN handles encryption and authentication, it uses the OpenSSL library quite extensively. Also, OpenVPN can use either UDP (User Datagram Protocol) or TCP (Transmission Control Protocol) to transmit data. If …